A recent security vulnerability in the Perfmatters plugin affected over 200,000 sites – including nearly 150 of our clients. Within minutes, we had protections in place, updates underway, and a plan to cover the edge cases. Here’s a behind-the-scenes look at how our team responded.
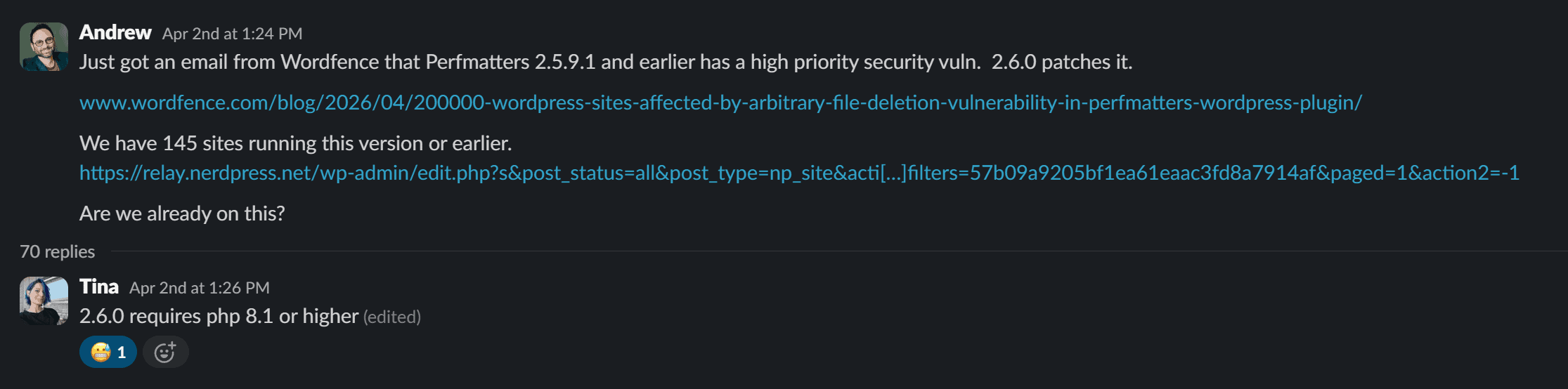
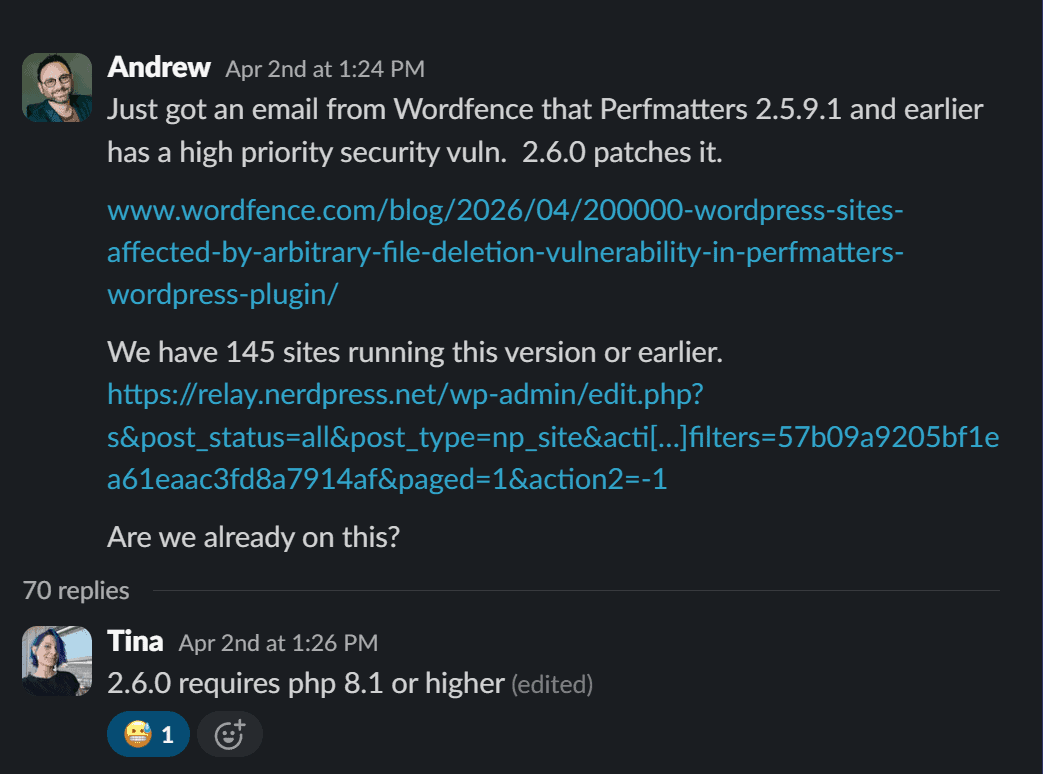
When we received an alert from Wordfence about the vulnerability, we jumped right in to investigate. This was a significant vulnerability, likely to be exploited quickly: Any logged-in user, including subscribers, could potentially delete critical files from a site. 😬
And once a vulnerability is disclosed publicly—along with what is effectively a roadmap for how to exploit it!—we have to move fast.
Before I continue, I want to be clear that I’m not writing this to throw the Perfmatters team under the bus – quite the opposite, in fact! We love Perfmatters and it’s a really helpful tool we use to help with our clients’ Core Web Vitals. Vulnerabilities are discovered on even the best software; what’s most important is how developers and teams respond.
The Timeline of Events
The alert came through early Thursday afternoon. We immediately confirmed the legitimacy and severity of the issue, and used our internal management tools to identify sites with the vulnerability. A hundred and forty-five sites were potentially affected.
A patched version was already available, so normally we would just update sites, make sure each one is working well, and be good to go.
But a significant complication appeared right away: The patched version of the plugin required at least PHP 8.1, and not all sites were there yet. (We’ve been working with our clients on getting their servers updated, but it’s a time-consuming process since versions of PHP may not be compatible with older themes or plugins.)
That certainly complicated matters, since it meant we couldn’t rely on a straightforward “update everyone right away and move on” approach. So we split the response into parallel tracks.
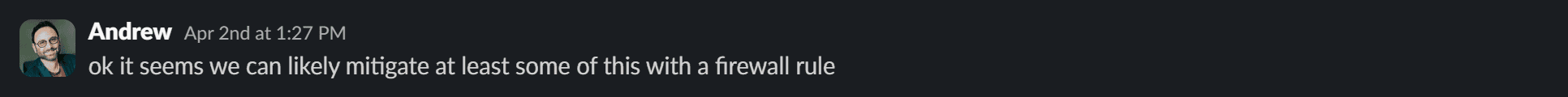
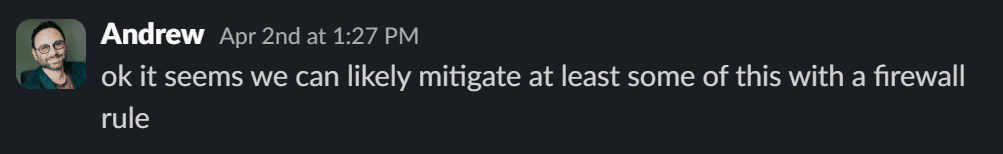
First, we focused on immediate protection. As Tina and our updates team were starting to update sites, our Cloudflare team used Wordfence’s technical analysis to implement a firewall rule designed to block the specific request patterns associated with the vulnerability.
That meant we were able to protect all our sites within seven minutes of triaging the issue!
We continued updating every site that could safely move to the patched version. Before the end of the day, the majority of affected sites had been secured through updates alone.
That left a smaller group of sites still running older PHP versions. We couldn’t install the official patch yet, but they were already shielded by the firewall rule, so we could relax a bit. Still, we didn’t want to rely on that long-term.
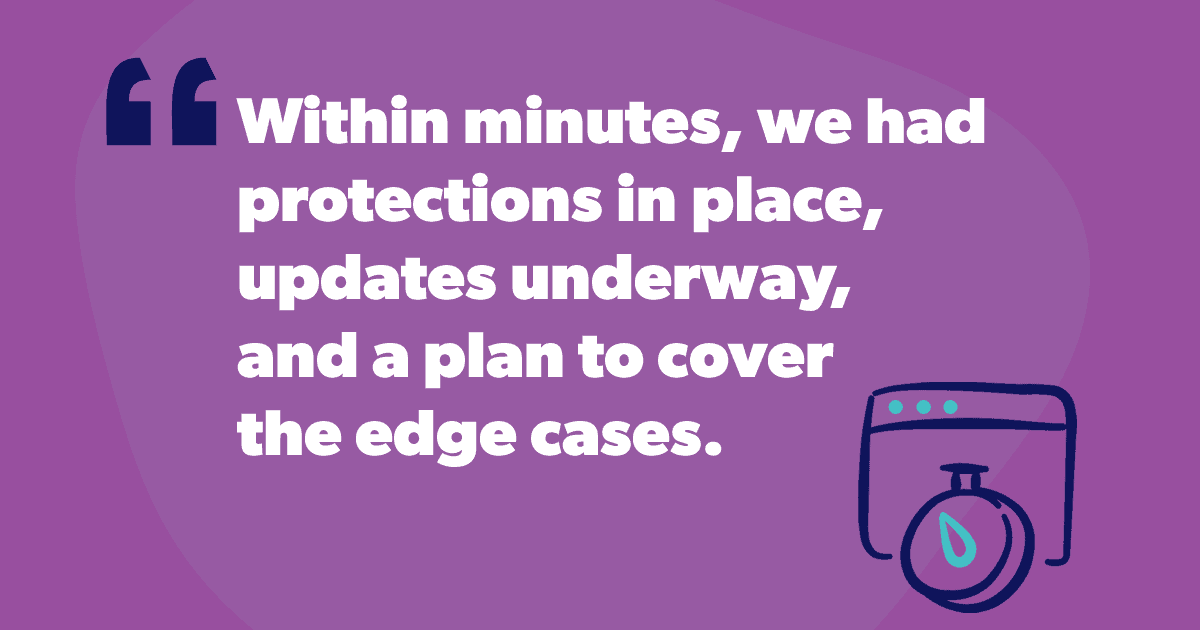
The next step was collaboration
On Friday we contacted the Perfmatters team and asked if they could provide a patched version compatible with older PHP environments. Brett responded quickly and confirmed they were working on it, and on Monday he shared a “legacy” build with the security fix that didn’t have the newer PHP requirement.
As soon as that was available, we rolled it out across the remaining sites.
From start to finish, this was a coordinated team effort: updates, firewall protections, client communication, and vendor collaboration all happening in parallel. It’s a good example of how we approach these situations: move quickly, reduce risk immediately, and then work toward a complete, long-term solution.
It’s also a reminder of how valuable collaboration in the WordPress ecosystem is. Plugin developers, security researchers, hosting environments, and support teams all play a role. In this case, the Perfmatters team was responsive and helpful (one of the reasons we love working with them!).
At the same time, we were also sharing what we were seeing with others in the WordPress community via the “Collaborators” Slack channel that we host in our workspace—which currently connects more than 70 people across 25 different companies—flagging edge cases, helping troubleshoot unexpected issues, and passing along interim solutions where we could.
(And the collaboration never ends: A follow-up bug in the patched release was causing issues with how Google crawled certain pages, and through collaboration we were able to help identify and work around that while they prepared a fix… but that’s a story for another time.😆)
Nothing about this was visible to most clients, which is exactly how it should be. There were no compromises on the sites we manage. Just a lot of coordinated, behind-the-scenes work to keep things that way.
This is the kind of work our team is built for, and something I’m really proud of. Rapid response, layered mitigation, and coordinated follow-through when security issues happen to keep everything running smoothly for our clients.
It’s also one example of what you can expect from NerdPress. See our WordPress Support Plans to learn more.